Let’s begin with my definition of security and privacy. I would define security as protection from direct threats, which are generally illegal. Privacy, I would define as protection against indirect threats. Here’s what I mean by this. If we think of these two in the physical world, we could consider security as preventing people from robbing or attacking you. There are tools to help accomplish this such as locks, guns, bright lights, and home security systems. Privacy would be preventing people from knowing or seeing things you don’t wish to share. Tools such as curtains, privacy fence, and closed doors are used to maintain privacy. The key concern with privacy is that you are not just protecting your dignity, but you’re protecting yourself against indirect threats. If someone gets embarrassing information about you, they might attempt to blackmail you. Or perhaps they have so much individually benign information (your DOB, address, mother’s maiden name, etc.) that they are able to steal your identity. Or, because passers by have no trouble seeing your state of the art home theatre system through your picture window, someone decides to rob you. This is why I define privacy as protecting against indirect threats. Particularly in the digital realm, there are indirect threats out there today, and there will undoubtedly be new ones crop up in the future, which we can guard against now.
If you read security and privacy articles (which are surprisingly hard to find) they often talk about Threat Models. This is a $10 word for knowing what you are defending, and who you’re defending it against. There are plenty of good write ups on what this means in the data protection industry. I’d recommend The Electronic Frontier Foundation and this article on yourultimatesecurity.guide if you want to understand threat modeling further. For this article, I’d like to look at it from a little different angle, and talk about general threats, and how we evaluate techniques and technologies against TYPES of threats that we all face.I think that most average users probably have pretty similar “threat profiles”. By looking at this framework, I think we can perhaps pass over some of the intensive threat modeling, and have a more general understanding of where our weaknesses are.
So let’s get into the meat here and look at what the possible threats are (based on living in the US in 2016). In the reading I’ve done, I’ve come up with five types of threats. I think these pretty well encompass all of the different types of groups that might be targeting someone. By beginning with this framework, I think it will help us to look at what we’re protecting against with a given technology or technique.
Here is my threat framework:
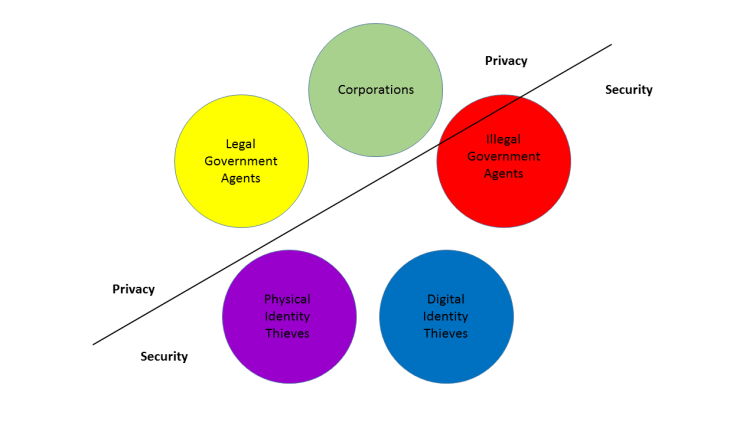
You’ll notice that I’ve got a lot going on here. There are five groups, which I’ll explain in more detail below. They each have a color, there’s no great symbolism to the colors, it’s just to make it easier to read. The order is important though. You’ll notice that there is a line going diagonally. In my mind, two of these threats are exclusively “Security” related, two are exclusively “privacy’ related, and one is some of both. Lets look at each of them in order of complexity:
Physical identity thieves
I put this as a separate heading, because the defenses against them are physical defenses, rather than digital. This is someone who snatches your wallet and uses your credit cards. Or someone who steals your smartphone and accesses your personal information. The key here is it’s a threat who has physical access to you, your devices and your data.
Digital identity thieves
This group has the same aims as the one above, but is those that DON’T have physical access to you or your devices. They’re hacking you, installing malware on your computer, spoofing websites, phishing, etc.
Legal Government agencies
This would include agencies that are following the law, and harassing you for some reason. Your local police department, the FBI, the IRS, the EPA, the FCC, etc. You may wonder why I list them as a threat. Hopefully, none of you are doing anything immoral that is also illegal. Unfortunately, there are tens of thousands of laws on the books, and not a single person on the planet can be absolutely certain what is and isn’t legal in a given jurisdiction. This can lead to people breaking laws on a regular basis that they aren’t even aware of. I don’t want anyone going to jail over “crimes” of that nature. There is also the chance that you’ll be falsely accused of something, or subject to an accidental S.W.A.T. raid. In all of these situations, it’s important to protect yourself against these legal assaults. It’s also important to acknowledge that these tools and legal protections do help bad people get away with bad things. Privacy and security tools can be used by rapists, murders, terrorists, etc. but those people are only a small portion of society. They also benefit from cars, public services, electricity, and a host of other good things. Just because a bad person uses a good tool to do bad things, is not an argument against that tool. Also, to be clear, while a government agency may be legally empowered, that does not mean that a particular agent is not acting either unethically or illegally. An example would be a police officer who pressures you to speak to them without legal representation. While that’s not necessarily illegal, it may be unethical (if they’re lying to you, which I believe IS legal) and it’s certainly against your best interests, whether or not you are innocent.
Corporations
Corporate entities, whether behemoths such as Google or WalMart or small local businesses have a tremendous incentive to use technology for sales and marketing strategies. It is becoming more and more critical that companies have apps, good websites, online storefronts, etc. As this happens, business owners (and/or managers) have realized that computers and the internet offer unprecedented opportunities for targeted marketing. As a result, everywhere you go on the internet sites that are trying to sell you something are collecting some level of detail about you, in order to market to you better and sell more product. On the simplest scale, as a blogger, I can track traffic on individual posts. I can see how many people look at specific webpages, and tailor content to match that. If I write a big post about broccoli, and only 2 people look at it, then the next day I write about the NSA and 20,000 people read it. That clues me in that I should write more about the NSA. On the opposite end of the spectrum is Google. Google is the largest data aggregator in human history. The reason they are able to offer so many free services is that they are scraping your interactions with them in order to build a profile on you that they can then use to sell extremely valuable ad space in their products. Now, as I have said before; I don’t hate Google. I think they are a company that has done some awesome things. Unfortunately, I think that as they’ve evolved (or perhaps exploded would be a better word) they (along with almost all other major internet companies) have developed revenue models that are fundamentally flawed, and at odds with a free society. Why is this dangerous? The first reason is that by allowing themselves access to all of your information, companies leave openings where malicious parties could hack in and steal your data. Most webmail now is encrypted in transit, so it’s safe from people intercepting, but the mailbox itself is left unencrypted, so that it’s easy for the provider to read your mail, this also makes it easier for someone else to break in and read your mail. The second reason is that these companies have generally been complicit with government mass surveillance projects such as PRISM. There’s a lot that’s unknown about these, and perhaps all of the past projects have been benign, legal and no problem. However, Facebook, et al will most likely continue to develop a profile on me for the rest of my life. If a government should come to power that DOES want to abuse that data, allowing companies to have it means it could eventually be taken from them. The final concern with this type of tracking is that it’s only benign if the people using it are benign. Facebook has done studies (without consent) that lead them to believe they can influence voter turnout. As far as we’ve been told, they’ve only done it to encourage general turn out. But if they can do that, can they also influence elections? Would we know if they were?
Illegal government agencies
Last, but certainly not least, we have agencies such as the NSA. To be clear, what I mean here is agencies that have been legally authorized, such as the NSA (and perhaps the CIA and FBI) but have then gone ‘off books’ and developed their own illegal activities. As mentioned in the previous section, it is possible that this has not happened to date in the US. I for one believe Edward Snowden’s wikileak information that shows that they have, but even if they have not; we know for absolute fact that there have been corrupt and despotic governments in other places and times who WOULD abuse the tremendous power of the internet. Despite our relatively safe and comfortable existence now (in the US at least) I believe we should work on building an internet ecosystem that has built in safeguards to keep it from being used as a weapon by any tyrannical government that should arise in the future. The risks from this are that government can easily target people based on things such as their beliefs, ethnicity, wealth, etc. when they have access to the vast troves of data that most of us leave on the internet these days. Imagine how the Facebook profiles of Jews and their friends could have been used in Nazi Germany in the 1930s and 40s.
Conclusion
My intent with this framework is to help us consider the different groups that might be interested in our data. As we look at different privacy technologies (VPN, Encrypted services, etc) they each protect against some or all of these groups. This is important for 2 reasons. First, if you’re actively trying to hide from a particular group, i.e., you’re a whistle blower or a political dissident under a repressive regime, you need to know if particular strategies will work for you. Second, I often see privacy or security features touted without acknowledging that they only protect your privacy/security in certain ways. For example, most webmail providers, such as Google and Yahoo have started to encrypt emails in transit. This is great! It does a lot to protect you against digital information theft, and even against some government snooping. However, it’s NOT the same thing as a fully encrypted system that protects you against the email provider reading your emails. Google, Yahoo, Hotmail, etc. can still scrape your emails for data about you. Therefore we could say it is a good SECURITY feature, but doesn’t necessarily improve your PRIVACY. I believe that the framework that I’ve laid out covers, in broad strokes, all of the types of threats you might face. My hope is that by thinking through how any given tool protects your relationship with each of these groups, you can better evaluate what you’re actually achieving with that tool. By using this framework to evaluate a technique or technology, then I believe you can have a more robust view of privacy and security.

One thought on “Security and Privacy”